TLS handshake
In order to establish a HTTPS communication channel the client and server must agree to use the same communication protocols. This negotiation is called a handshake. During this process certificates and keys are exchanged. RSA-based TLS uses a set of asymmetric keys to encrypt/decrypt data in transit.
-
Private key
A private key is known only the server side in the HTTPS communication.
-
Public key
The public key is known to all clients initiating the HTTPS communication. The public key is stored in a file known as a digital certificate.
TLS Handshake Process
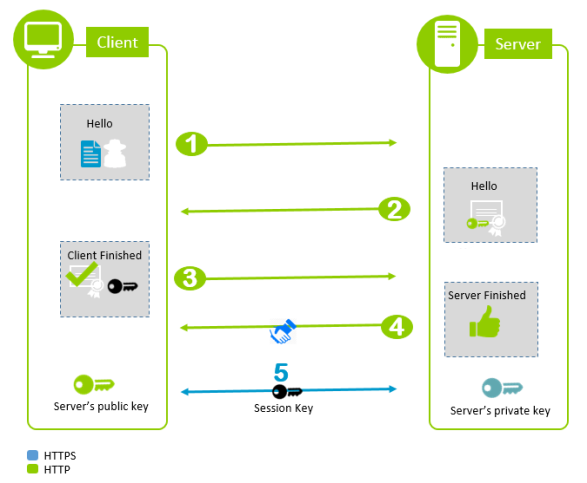
The TLS handshake presented here is simplified for the sake of clarity and occurs after all components have been installed and configured.
-
Client Hello: Client initiates HTTPS communication.
Initiated by the client computer, the request for HTTPS communication includes the protocols and cipher suites supported by the client.
-
Server Hello: Server selects protocol/cipher suite and sends its certificate.
Based on the request sent by the client, the server responds by telling the client the key exchange method, cipher suite, and hash it wants to use.
The server sends its server certificate to the client. The server certificate identifies the server to the client, and includes its public key, its hostname, and other identifying information.
-
Client agrees to encrypted communication.
If the client trusts the CA that signed the server certificate sent by the server, it sends a message containing the message authentication code that it agrees to use HTTPS.
-
Server agrees to encrypted communication.
-
Encrypted communication begins.
During this phase of the dataflow, the asymmetric keys are used to securely transfer a one-time symmetric session key, which is used later to encrypt the HTTPS communication when establishing a secured channel.
With asymmetric keys:
-
The server uses its private key to encrypt and decrypt data.
-
The client uses a public key to encrypt and decrypt data.
With the symmetric key, both client and server use the same key to encrypt and decrypt the communication.
-